使用AWS CLI从命令行解密密文时,密文可以顺利解密:
$ aws kms decrypt --ciphertext-blob fileb://encrypted-secrets --output text --query Plaintext --region us-east-1 | base64 --decode > decryped-secrets
当尝试从js脚本执行此操作时,此解密操作也可以在本地工作:
#!/usr/local/bin/node
const fs = require('fs');
const AWS = require('aws-sdk');
const kms = new AWS.KMS({region:'us-east-1'});
const secretPath = './encrypted-secrets';
const encryptedSecret = fs.readFileSync(secretPath);
const params = {
CiphertextBlob: encryptedSecret
};
kms.decrypt(params, function(err, data) {
if (err) {
console.log(err, err.stack);
} else {
const decryptedScret = data['Plaintext'].toString();
console.log('decrypted secret', decryptedScret);
}
});
然而,当尝试使用几乎完全相同的代码在 AWS Lambda 函数的上下文中运行时,函数调用会导致超时:
'use strict';
const zlib = require('zlib');
const mysql = require('mysql');
const fs = require('fs');
const AWS = require('aws-sdk');
const kms = new AWS.KMS({region:'us-east-1'});
const secretPath = './encrypted-secrets';
const encryptedSecret = fs.readFileSync(secretPath);
const params = {
CiphertextBlob: encryptedSecret
};
exports.handler = (event, context, callback) => {
kms.decrypt(params, (err, data) => {
if (err) {
console.log(err, err.stack);
return callback(err);
} else {
const decryptedScret = data['Plaintext'].toString();
console.log('decrypted secret', decryptedScret);
return callback(null, `Successfully processed ${parsed.logEvents.length} log events.`);
}
});
};
超时日志:
START RequestId: start-request-id-redacted Version: $LATEST
END RequestId: end-request-id-redacted
REPORT RequestId: report-requested-id-redacted Duration: 10002.43 ms Billed Duration: 10000 ms Memory Size: 128 MB Max Memory Used: 18 MB
2016-11-13T19:22:28.774Z task-id-redacted Task timed out after 10.00 seconds
注:
- 如果我注释掉对
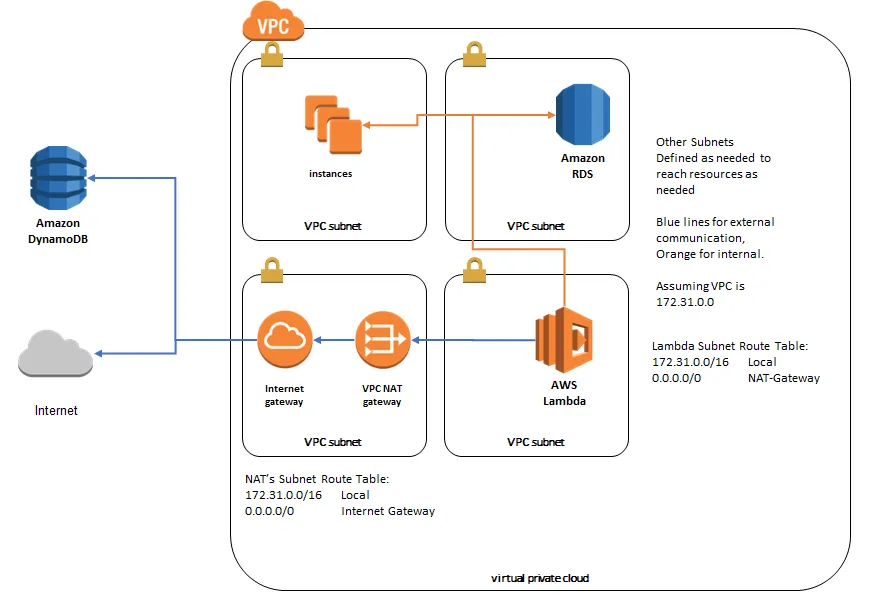
kms.decrypt的调用并尝试使用console.log输出params或其他任何东西,这些值将被输出而没有问题。似乎在kms.decrypt调用中存在某种问题,并且没有超时之外的实际错误返回。 - 附加到调用 lambda 函数的角色上的策略包括附加的策略
AWSLambdaVPCAccessExecutionRole,以及以下附加的内联策略:
policygen-lambda_basic_execution_and_kms_decrypt-201611131221:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "sid-redacted",
"Effect": "Allow",
"Action": [
"kms:Decrypt"
],
"Resource": [
"arn:aws:kms:us-east-1:account-redacted:key/key-id-redacted"
]
}
]
}
- 我已经从代码中删除了任何识别信息。