我尝试使用这篇文章中概述的原理,用Python 3编写了一个基本的TCP防火墙穿透程序。但是,我无法让任何东西连接上。下面是代码:
#!/usr/bin/python3
import sys
import socket
import _thread as thread
def client():
c = socket.socket()
c.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
c.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEPORT, 1)
c.bind((socket.gethostbyname(socket.gethostname()), int(sys.argv[3])))
while(c.connect_ex((sys.argv[1], int(sys.argv[2])))):
pass
print("connected!")
thread.interrupt_main()
def server():
c = socket.socket()
c.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
c.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEPORT, 1)
c.bind((socket.gethostbyname(socket.gethostname()), int(sys.argv[3])))
c.listen(5)
c.accept()
print("connected!")
thread.interrupt_main()
def main():
thread.start_new_thread(client, ())
thread.start_new_thread(server, ())
while True:
pass
if __name__ == '__main__':
main()
我决定在我的本地机器上尝试这个打洞工具,以便我可以捕获两个实例发送的所有流量。我首先设置了一个回环防火墙:
iptables -A INPUT -i lo -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -A INPUT -i lo -j DROP
然后我启动了两个脚本的副本:
left$ ./tcphole.py localhost 20012 20011
并且
right$ ./tcphole.py localhost 20011 20012
我可以根据Wireshark看到SYN数据包在双向传输:
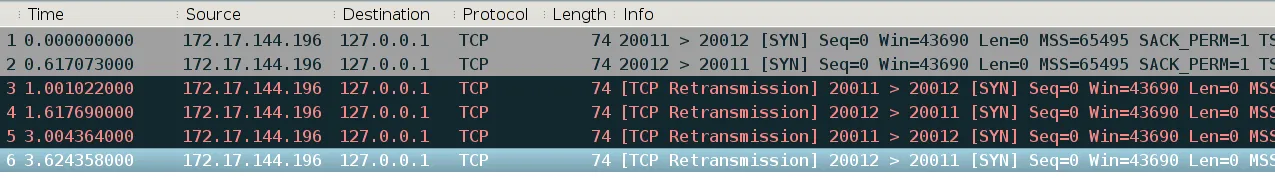 但是没有任何东西打印“connected!”。我做错了什么?
但是没有任何东西打印“connected!”。我做错了什么?