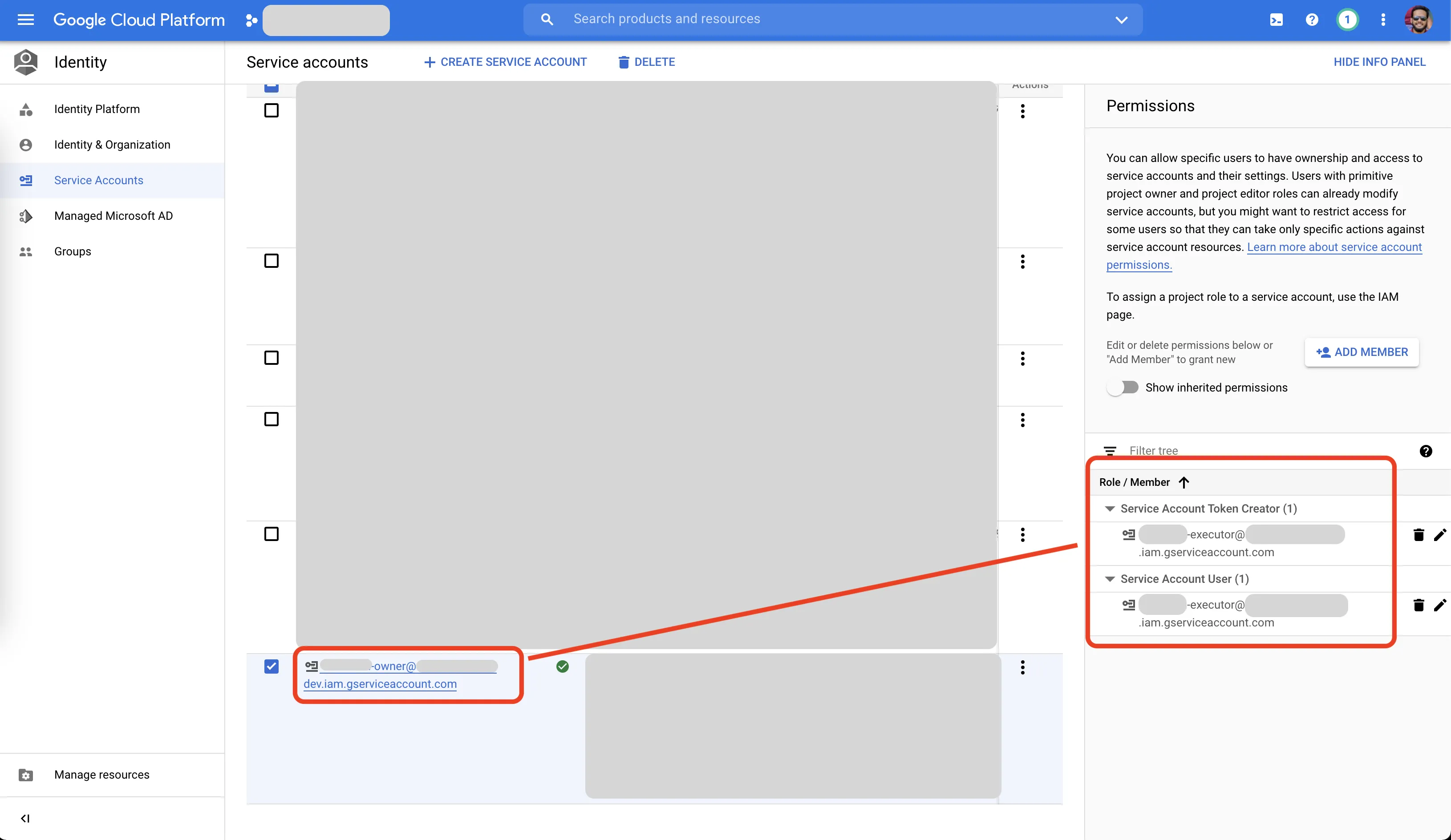
我在Google Cloud Platform(GCP)项目中有2个ServiceAccounts。
- owner(所有者)
- executor(执行者)
owner ServiceAccount被附加了1个项目级别的角色:
- "Owner" - 用于该项目
executor ServiceAccount仅被附加了2个特定角色(如下所示):
- "Service Account Token Creator" - 在Owner ServiceAccount 上
- "Service Account User" - 在Owner ServiceAccount 上
现在,我有Executor ServiceAccount的JSON密钥文件。我将使用该凭据文件来“冒充”Owner ServiceAccount。然后我将运行gcloud命令。
这是我正在做的事情。
#!/bin/bash
# --------------------------------------------------------------
export GOOGLE_APPLICATION_CREDENTIALS="$(pwd)/my-executor-sa-key.json"
echo $GOOGLE_APPLICATION_CREDENTIALS
cat $GOOGLE_APPLICATION_CREDENTIALS
OWNER_EMAIL="owner@my-gcp-project.iam.gserviceaccount.com"
echo $OWNER_EMAIL
# --------------------------------------------------------------
CLUSTER="my-k8s-cluster"
ZONE="asia-east1-a"
PROJECT="my-gcp-project"
MY_COMMAND="gcloud container clusters get-credentials ${CLUSTER} --zone ${ZONE} --project ${PROJECT} --impersonate-service-account=${OWNER_EMAIL}"
echo $MY_COMMAND
# --------------------------------------------------------------
`$MY_COMMAND`
# --------------------------------------------------------------
在运行上面的代码后,这是我得到的输出结果。
# --------------------------------------------------------------
/Users/rakib/tmp/my-executor-sa-key.json
{
"type": "service_account",
"project_id": "my-gcp-project",
"private_key_id": "3208--------------------------------5d63",
"private_key": "-----BEGIN PRIVATE KEY-----\nMIIEv\n----\nEAE9S\n-----END PRIVATE KEY-----\n",
"client_email": "executor@my-gcp-project.iam.gserviceaccount.com",
"client_id": "1099--------------5533",
"auth_uri": "https://accounts.google.com/o/oauth2/auth",
"token_uri": "https://oauth2.googleapis.com/token",
"auth_provider_x509_cert_url": "https://www.googleapis.com/oauth2/v1/certs",
"client_x509_cert_url": "https://www.googleapis.com/robot/v1/metadata/x509/executor%40my-gcp-project.iam.gserviceaccount.com"
}
owner@my-gcp-project.iam.gserviceaccount.com
# --------------------------------------------------------------
gcloud container clusters get-credentials my-k8s-cluster --zone asia-east1-a --project my-gcp-project --impersonate-service-account=owner@my-gcp-project.iam.gserviceaccount.com
# --------------------------------------------------------------
WARNING: This command is using service account impersonation. All API calls will be executed as [owner@my-gcp-project.iam.gserviceaccount.com].
ERROR: (gcloud.container.clusters.get-credentials) Failed to impersonate [owner@my-gcp-project.iam.gserviceaccount.com]. Make sure the account that's trying to impersonate it has access to the service account itself and the "roles/iam.serviceAccountTokenCreator" role.
我在这里错过了什么?我确实已经将Executor ServiceAccount授予Owner ServiceAccount的roles/iam.serviceAccountTokenCreator角色。
为什么它不能进行模拟呢?