我的公司有两个AWS账户。在第一个账户(我们称之为playground),我拥有完全的管理员权限。而在第二个账户(我们称之为production),我只有有限的IAM权限。
我在这两个账户上都启用了AWS Config(使用附录中的terraform文件)。
- 在playground上,它运行顺畅,一切都很好。
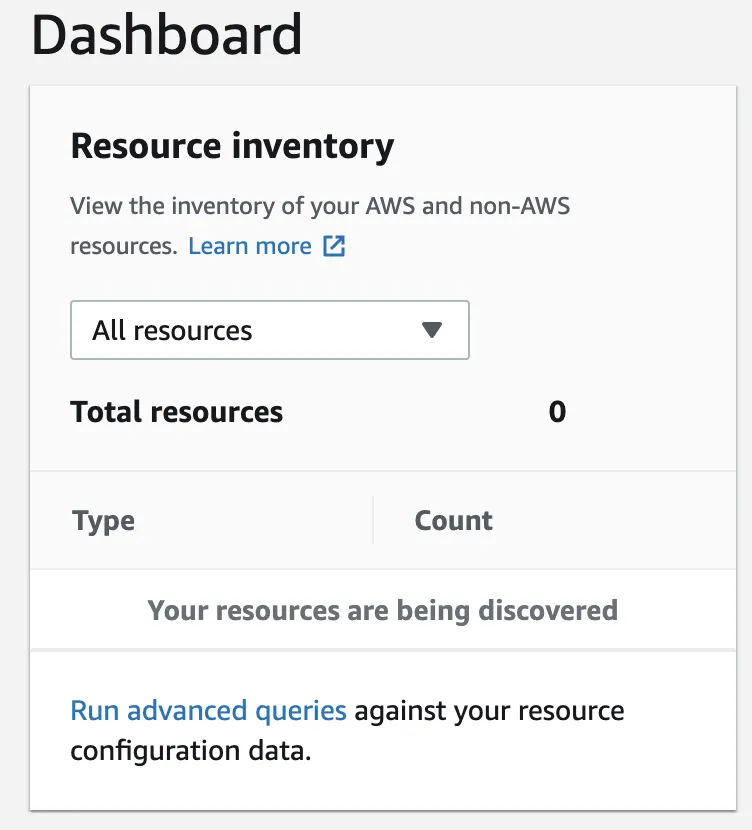
- 而在production上,则失败了。更具体地说,它未能检测到该账户的资源,并显示如下所示的消息“Your resources are being discovered”,如下面的屏幕截图所示。
我最初怀疑这可能是一个IAM角色权限问题。
例如运行:
aws configservice list-discovered-resources --resource-type AWS::EC2::SecurityGroup --profile playground会给我返回在playground上通过AWS Config发现的安全组列表(基本上就是我在控制台仪表板上看到的内容)。
另一方面:
aws configservice list-discovered-resources --resource-type AWS::EC2::SecurityGroup --profile production则返回一个空列表(尽管有安全组。在其他类型,如AWS::EC2::Instance时也是同样的结果)。
{
"resourceIdentifiers": []
}
由于IAM角色确实拥有执行describe API调用的权限,我排除了IAM权限的怀疑。它可以工作,只是返回null。
可能是AWS Config角色AWSServiceRoleForConfig导致的问题吗?这没有意义。由于这是一个服务链接角色,它默认应该具有所有必需的权限。(不过将策略追加到帖子末尾)
现在是奇怪的部分:
我的规则验证一些资源(例如EFS),但会抛出此消息:指定的资源要么未知,要么未被发现。
我仍然怀疑这可能是一个IAM问题,但我无法弄清楚发生了什么。我已经为此苦苦挣扎了几天,真的需要一些帮助。
根据官方文档:
AWS Config通过调用描述或列出您帐户中每个资源的API调用来跟踪所有资源的更改。该服务使用相同的API调用来捕获所有相关资源的配置详细信息。
config.tf
# Create the configuration recorder
resource "aws_config_configuration_recorder" "default" {
name = "default-recorder"
role_arn = "arn:aws:iam::${var.account_id}:role/aws-service-role/config.amazonaws.com/AWSServiceRoleForConfig"
recording_group {
all_supported = true
include_global_resource_types = true
}
}
# Enable the configuration recorder
resource "aws_config_configuration_recorder_status" "default" {
name = aws_config_configuration_recorder.default.name
is_enabled = true
depends_on = [aws_config_delivery_channel.default]
}
# Connect AWS Config to the S3 bucket
resource "aws_config_delivery_channel" "default" {
name = "default-channel"
s3_bucket_name = "central-config-bucket" # Central S3 bucket
depends_on = [aws_config_configuration_recorder.default]
}
# Deploy the default HIPAA compliance comformance pack
resource "aws_config_conformance_pack" "hipaa" {
name = "operational-best-practices-for-HIPAA-Security"
template_body = data.http.conformance_pack.body
}
data "http" "conformance_pack" {
url = "https://raw.githubusercontent.com/awslabs/aws-config-rules/master/aws-config-conformance-packs/Operational-Best-Practices-for-HIPAA-Security.yaml"
}
resource "aws_config_aggregate_authorization" "main" {
account_id = "************"
region = "eu-central-1"
}
默认的 AWSServiceRoleForConfig 策略:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"acm:DescribeCertificate",
"acm:ListCertificates",
"acm:ListTagsForCertificate",
"apigateway:GET",
"application-autoscaling:DescribeScalableTargets",
"application-autoscaling:DescribeScalingPolicies",
"autoscaling:DescribeAutoScalingGroups",
"autoscaling:DescribeLaunchConfigurations",
"autoscaling:DescribeLifecycleHooks",
"autoscaling:DescribePolicies",
"autoscaling:DescribeScheduledActions",
"autoscaling:DescribeTags",
"backup:DescribeBackupVault",
"backup:DescribeRecoveryPoint",
"backup:GetBackupPlan",
"backup:GetBackupSelection",
"backup:GetBackupVaultAccessPolicy",
"backup:GetBackupVaultNotifications",
"backup:ListBackupPlans",
"backup:ListBackupSelections",
"backup:ListBackupVaults",
"backup:ListRecoveryPointsByBackupVault",
"backup:ListTags",
"cloudformation:DescribeType",
"cloudformation:ListTypes",
"cloudfront:ListTagsForResource",
"cloudtrail:DescribeTrails",
"cloudtrail:GetEventSelectors",
"cloudtrail:GetTrailStatus",
"cloudtrail:ListTags",
"cloudwatch:DescribeAlarms",
"codepipeline:GetPipeline",
"codepipeline:GetPipelineState",
"codepipeline:ListPipelines",
"config:BatchGet*",
"config:Describe*",
"config:Get*",
"config:List*",
"config:Put*",
"config:Select*",
"dax:DescribeClusters",
"dms:DescribeReplicationInstances",
"dms:DescribeReplicationSubnetGroups",
"dms:ListTagsForResource",
"dynamodb:DescribeContinuousBackups",
"dynamodb:DescribeLimits",
"dynamodb:DescribeTable",
"dynamodb:ListTables",
"dynamodb:ListTagsOfResource",
"ec2:Describe*",
"ec2:GetEbsEncryptionByDefault",
"ecr:DescribeRepositories",
"ecr:GetLifecyclePolicy",
"ecr:GetRepositoryPolicy",
"ecr:ListTagsForResource",
"ecs:DescribeClusters",
"ecs:DescribeServices",
"ecs:DescribeTaskDefinition",
"ecs:DescribeTaskSets",
"ecs:ListClusters",
"ecs:ListServices",
"ecs:ListTagsForResource",
"ecs:ListTaskDefinitions",
"eks:DescribeCluster",
"eks:DescribeNodegroup",
"eks:ListClusters",
"eks:ListNodegroups",
"elasticache:DescribeCacheClusters",
"elasticache:DescribeCacheParameterGroups",
"elasticache:DescribeCacheSubnetGroups",
"elasticache:DescribeReplicationGroups",
"elasticfilesystem:DescribeAccessPoints",
"elasticfilesystem:DescribeBackupPolicy",
"elasticfilesystem:DescribeFileSystemPolicy",
"elasticfilesystem:DescribeFileSystems",
"elasticfilesystem:DescribeLifecycleConfiguration",
"elasticfilesystem:DescribeMountTargets",
"elasticfilesystem:DescribeMountTargetSecurityGroups",
"elasticloadbalancing:DescribeListeners",
"elasticloadbalancing:DescribeLoadBalancerAttributes",
"elasticloadbalancing:DescribeLoadBalancerPolicies",
"elasticloadbalancing:DescribeLoadBalancers",
"elasticloadbalancing:DescribeRules",
"elasticloadbalancing:DescribeTags",
"elasticmapreduce:DescribeCluster",
"elasticmapreduce:DescribeSecurityConfiguration",
"elasticmapreduce:GetBlockPublicAccessConfiguration",
"elasticmapreduce:ListClusters",
"elasticmapreduce:ListInstances",
"es:DescribeElasticsearchDomain",
"es:DescribeElasticsearchDomains",
"es:ListDomainNames",
"es:ListTags",
"guardduty:GetDetector",
"guardduty:GetFindings",
"guardduty:GetMasterAccount",
"guardduty:ListDetectors",
"guardduty:ListFindings",
"iam:GenerateCredentialReport",
"iam:GetAccountAuthorizationDetails",
"iam:GetAccountPasswordPolicy",
"iam:GetAccountSummary",
"iam:GetCredentialReport",
"iam:GetGroup",
"iam:GetGroupPolicy",
"iam:GetPolicy",
"iam:GetPolicyVersion",
"iam:GetRole",
"iam:GetRolePolicy",
"iam:GetUser",
"iam:GetUserPolicy",
"iam:ListAttachedGroupPolicies",
"iam:ListAttachedRolePolicies",
"iam:ListAttachedUserPolicies",
"iam:ListEntitiesForPolicy",
"iam:ListGroupPolicies",
"iam:ListGroupsForUser",
"iam:ListInstanceProfilesForRole",
"iam:ListPolicyVersions",
"iam:ListRolePolicies",
"iam:ListUserPolicies",
"iam:ListVirtualMFADevices",
"kinesis:DescribeStreamSummary",
"kinesis:ListStreams",
"kinesis:ListTagsForStream",
"kms:DescribeKey",
"kms:GetKeyPolicy",
"kms:GetKeyRotationStatus",
"kms:ListKeys",
"kms:ListResourceTags",
"lambda:GetAlias",
"lambda:GetFunction",
"lambda:GetPolicy",
"lambda:ListAliases",
"lambda:ListFunctions",
"logs:DescribeLogGroups",
"organizations:DescribeOrganization",
"rds:DescribeDBClusters",
"rds:DescribeDBClusterSnapshotAttributes",
"rds:DescribeDBClusterSnapshots",
"rds:DescribeDBInstances",
"rds:DescribeDBSecurityGroups",
"rds:DescribeDBSnapshotAttributes",
"rds:DescribeDBSnapshots",
"rds:DescribeDBSubnetGroups",
"rds:DescribeEventSubscriptions",
"rds:ListTagsForResource",
"redshift:DescribeClusterParameterGroups",
"redshift:DescribeClusterParameters",
"redshift:DescribeClusters",
"redshift:DescribeClusterSecurityGroups",
"redshift:DescribeClusterSnapshots",
"redshift:DescribeClusterSubnetGroups",
"redshift:DescribeEventSubscriptions",
"redshift:DescribeLoggingStatus",
"route53:GetHostedZone",
"route53:ListHostedZones",
"route53:ListHostedZonesByName",
"route53:ListResourceRecordSets",
"route53:ListTagsForResource",
"s3:GetAccelerateConfiguration",
"s3:GetAccessPoint",
"s3:GetAccessPointPolicy",
"s3:GetAccessPointPolicyStatus",
"s3:GetAccountPublicAccessBlock",
"s3:GetBucketAcl",
"s3:GetBucketCORS",
"s3:GetBucketLocation",
"s3:GetBucketLogging",
"s3:GetBucketNotification",
"s3:GetBucketObjectLockConfiguration",
"s3:GetBucketPolicy",
"s3:GetBucketPublicAccessBlock",
"s3:GetBucketRequestPayment",
"s3:GetBucketTagging",
"s3:GetBucketVersioning",
"s3:GetBucketWebsite",
"s3:GetEncryptionConfiguration",
"s3:GetLifecycleConfiguration",
"s3:GetReplicationConfiguration",
"s3:ListAccessPoints",
"s3:ListAllMyBuckets",
"s3:ListBucket",
"sagemaker:DescribeCodeRepository",
"sagemaker:DescribeEndpointConfig",
"sagemaker:DescribeNotebookInstance",
"sagemaker:ListCodeRepositories",
"sagemaker:ListEndpointConfigs",
"sagemaker:ListNotebookInstances",
"sagemaker:ListTags",
"secretsmanager:ListSecrets",
"secretsmanager:ListSecretVersionIds",
"securityhub:describeHub",
"shield:DescribeDRTAccess",
"shield:DescribeProtection",
"shield:DescribeSubscription",
"sns:GetTopicAttributes",
"sns:ListSubscriptions",
"sns:ListTagsForResource",
"sns:ListTopics",
"sqs:GetQueueAttributes",
"sqs:ListQueues",
"sqs:ListQueueTags",
"ssm:DescribeAutomationExecutions",
"ssm:DescribeDocument",
"ssm:GetAutomationExecution",
"ssm:GetDocument",
"ssm:ListDocuments",
"storagegateway:ListGateways",
"storagegateway:ListVolumes",
"support:DescribeCases",
"tag:GetResources",
"waf-regional:GetLoggingConfiguration",
"waf-regional:GetWebACL",
"waf-regional:GetWebACLForResource",
"waf:GetLoggingConfiguration",
"waf:GetWebACL",
"wafv2:GetLoggingConfiguration"
],
"Resource": "*"
}
]
}
AWSServiceRoleForConfig第一次不会自动激活。您需要手动将其添加到 AWS 配置中。然后它就能正常工作了。@Marcin - Dimi