这很接近你所寻找的内容。有关更多详细信息,请参见
源代码。使用
Get-ACL的访问控制列表不像高级安全设置中的
有效访问那样易于阅读,我认为这是无法避免的。但是,一旦习惯了它,当你知道自己在寻找什么时,
Get-ACL会提供更多详细信息并可筛选ACL以获取所需内容。
function Get-EffectiveAccess {
[CmdletBinding()]
param(
[Parameter(Mandatory, ValueFromPipeline, ValueFromPipelineByPropertyName)]
[ValidatePattern('(?:(CN=([^,]*)),)?(?:((?:(?:CN|OU)=[^,]+,?)+),)?((?:DC=[^,]+,?)+)$')]
[alias('DistinguishedName')]
[string] $Identity,
[parameter()]
[alias('Domain')]
[string] $Server
)
begin {
$guid = [guid]::Empty
$GUIDMap = @{}
if($PSBoundParameters.ContainsKey('Server')) {
$domain = Get-ADRootDSE -Server $Server
}
else {
$domain = Get-ADRootDSE
}
$params = @{
SearchBase = $domain.schemaNamingContext
LDAPFilter = '(schemaIDGUID=*)'
Properties = 'name', 'schemaIDGUID'
ErrorAction = 'SilentlyContinue'
}
$adObjParams = @{
Properties = 'nTSecurityDescriptor'
}
if($PSBoundParameters.ContainsKey('Server')) {
$params['Server'] = $Server
$adObjParams['Server'] = $Server
}
$schemaIDs = Get-ADObject @params
$params['SearchBase'] = "CN=Extended-Rights,$($domain.configurationNamingContext)"
$params['LDAPFilter'] = '(objectClass=controlAccessRight)'
$params['Properties'] = 'name', 'rightsGUID'
$extendedRigths = Get-ADObject @params
foreach($i in $schemaIDs) {
if(-not $GUIDMap.ContainsKey([guid] $i.schemaIDGUID)) {
$GUIDMap.Add([guid] $i.schemaIDGUID, $i.name)
}
}
foreach($i in $extendedRigths) {
if(-not $GUIDMap.ContainsKey([guid] $i.rightsGUID)) {
$GUIDMap.Add([guid] $i.rightsGUID, $i.name)
}
}
}
process {
try {
$adObjParams['Identity'] = $Identity
$object = Get-ADObject @adObjParams
foreach($acl in $object.nTSecurityDescriptor.Access) {
if($guid.Equals($acl.ObjectType)) {
$objectType = 'All Objects (Full Control)'
}
elseif($GUIDMap.ContainsKey($acl.ObjectType)) {
$objectType = $GUIDMap[$acl.ObjectType]
}
else {
$objectType = $acl.ObjectType
}
if($guid.Equals($acl.InheritedObjectType)) {
$inheritedObjType = 'Applied to Any Inherited Object'
}
elseif($GUIDMap.ContainsKey($acl.InheritedObjectType)) {
$inheritedObjType = $GUIDMap[$acl.InheritedObjectType]
}
else {
$inheritedObjType = $acl.InheritedObjectType
}
[PSCustomObject]@{
Name = $object.Name
IdentityReference = $acl.IdentityReference
AccessControlType = $acl.AccessControlType
ActiveDirectoryRights = $acl.ActiveDirectoryRights
ObjectType = $objectType
InheritedObjectType = $inheritedObjType
InheritanceType = $acl.InheritanceType
IsInherited = $acl.IsInherited
}
}
}
catch {
$PSCmdlet.WriteError($_)
}
}
}
例子
- 获取名为
ExampleOU的组织单位的有效访问权限:
Get-ADOrganizationalUnit -Filter "Name -eq 'ExampleOU'" |
Get-EffectiveAccess | Out-GridView
- 获取受信任域上名为
ExampleOU的组织单位的有效访问权限:
Get-ADOrganizationalUnit -Filter "Name -eq 'ExampleOU'" -Server trustedDomain |
Get-EffectiveAccess -Server trustedDomain | Out-GridView
- 使用OU的
DistinguishedName属性,方法同上:
Get-EffectiveAccess -Identity 'OU=ExampleOU,DC=domainName,DC=com' | Out-GridView
- 将名为
exampleGroup的组的有效访问权限存储在一个变量中:
$effectiveAccess = Get-ADGroup exampleGroup | Get-EffectiveAccess
Get-ADOrganizationalUnit -Filter * | Select -First 10 |
Get-EffectiveAccess | Out-GridView
示例
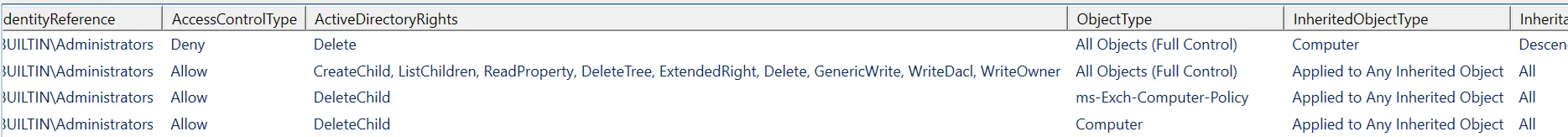
供参考,以下是使用 Get-ACL 命令查看完全控制权限的效果:
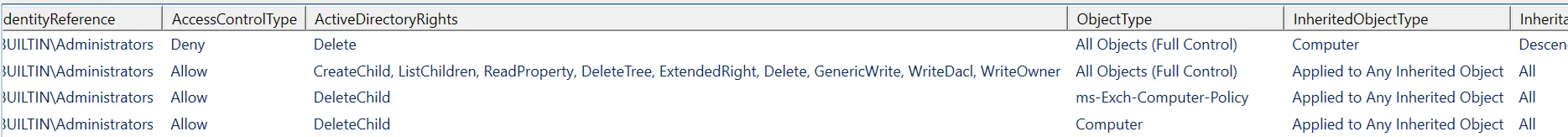
相比之下,BUILTIN\Administrators 对此 OU 具有写入权限,但没有完全控制权限:
 我正在尝试使用Powershell来实现这一点。我已经尝试过dsacls和Get-Acls,但这些都没有给出有效的权限。这两者都给出了“谁有访问/权限”,而这不同于“谁拥有什么有效权限”。它们也没有列出提供有效访问背景的所有细节。
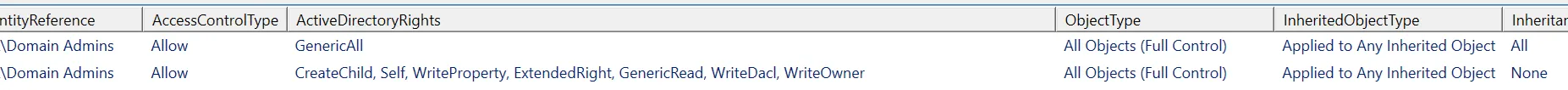
我正在尝试使用Powershell来实现这一点。我已经尝试过dsacls和Get-Acls,但这些都没有给出有效的权限。这两者都给出了“谁有访问/权限”,而这不同于“谁拥有什么有效权限”。它们也没有列出提供有效访问背景的所有细节。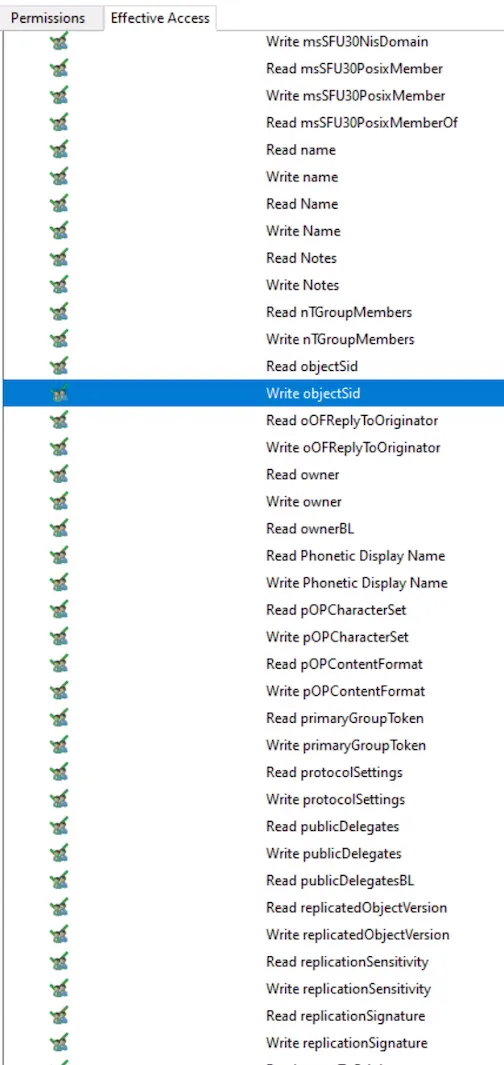 当我通过Get-ACL拉取域管理员对其中一个OU的权限时,解析ObjectType和InheritedObjectType中的值(使用Santiago Squarzon提到的get-effective access函数)后,我得到-
当我通过Get-ACL拉取域管理员对其中一个OU的权限时,解析ObjectType和InheritedObjectType中的值(使用Santiago Squarzon提到的get-effective access函数)后,我得到-
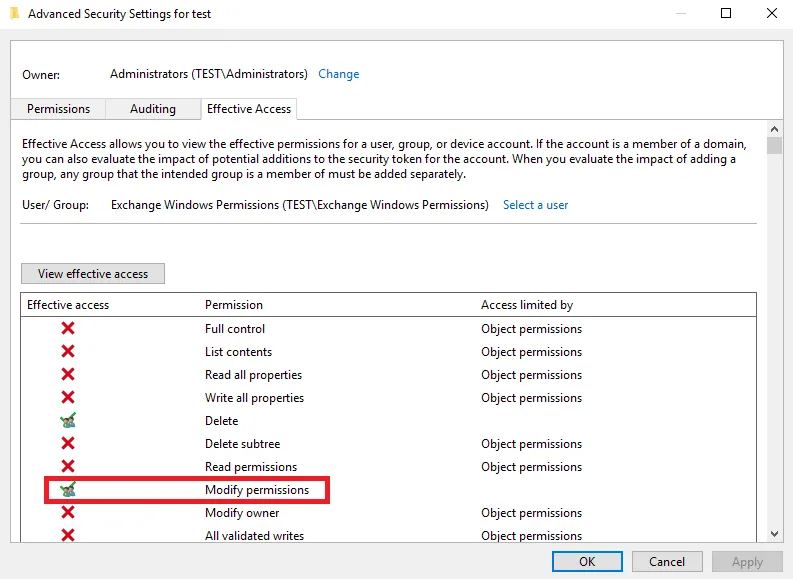
 而UI有效访问显示-
而UI有效访问显示-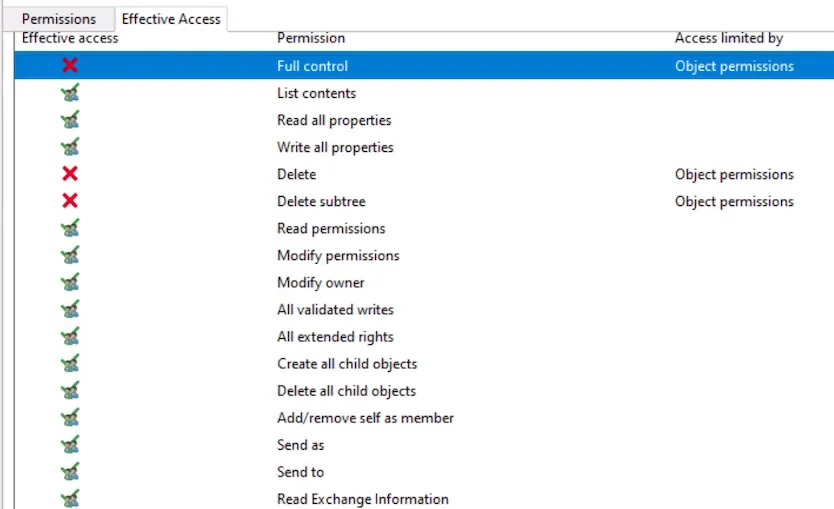 我的最终目标是使用powershell获取上述屏幕截图中的所有权限。
我的最终目标是使用powershell获取上述屏幕截图中的所有权限。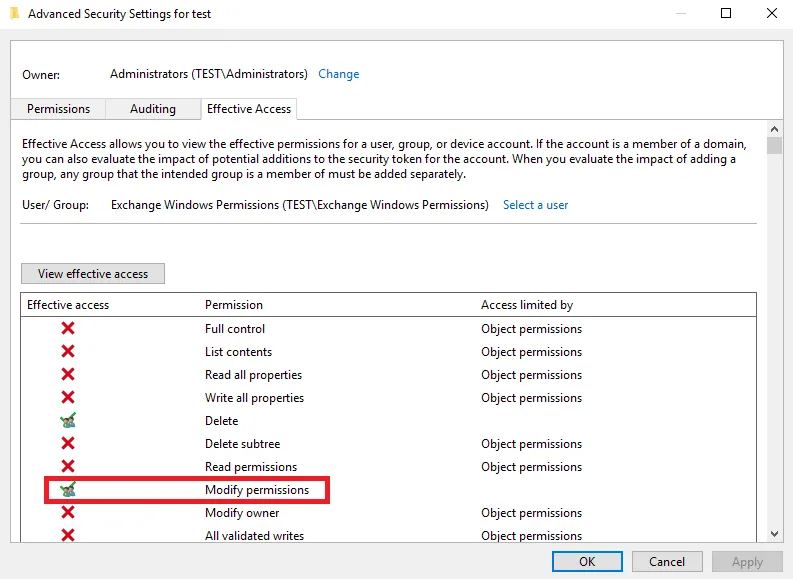 我正在尝试使用Powershell来实现这一点。我已经尝试过dsacls和Get-Acls,但这些都没有给出有效的权限。这两者都给出了“谁有访问/权限”,而这不同于“谁拥有什么有效权限”。它们也没有列出提供有效访问背景的所有细节。
我正在尝试使用Powershell来实现这一点。我已经尝试过dsacls和Get-Acls,但这些都没有给出有效的权限。这两者都给出了“谁有访问/权限”,而这不同于“谁拥有什么有效权限”。它们也没有列出提供有效访问背景的所有细节。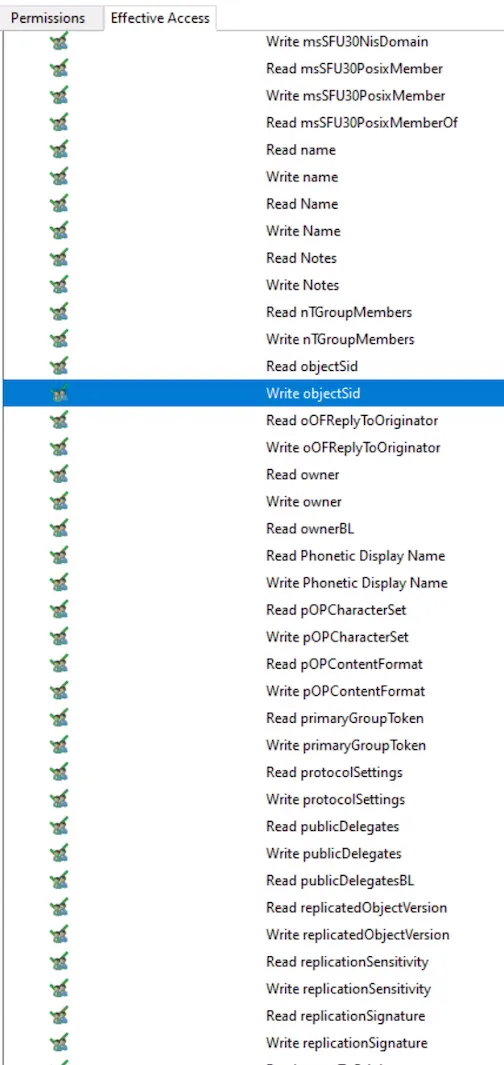 当我通过Get-ACL拉取域管理员对其中一个OU的权限时,解析ObjectType和InheritedObjectType中的值(使用Santiago Squarzon提到的get-effective access函数)后,我得到-
当我通过Get-ACL拉取域管理员对其中一个OU的权限时,解析ObjectType和InheritedObjectType中的值(使用Santiago Squarzon提到的get-effective access函数)后,我得到-
 而UI有效访问显示-
而UI有效访问显示-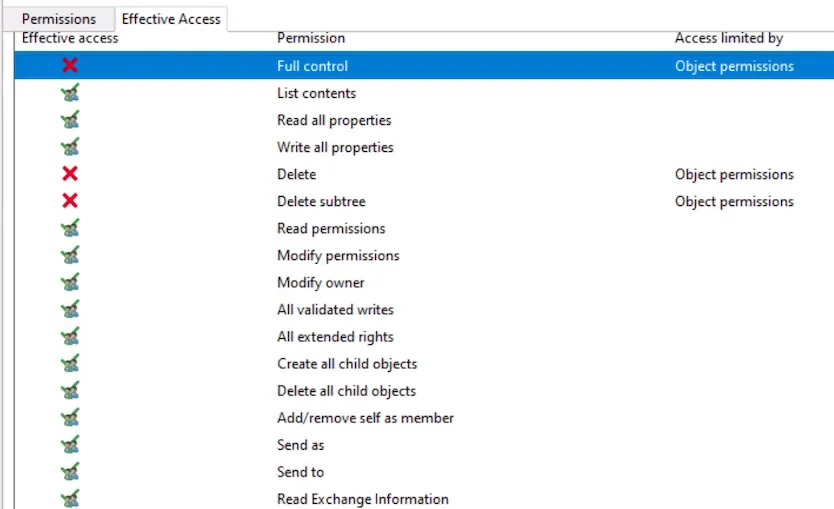 我的最终目标是使用powershell获取上述屏幕截图中的所有权限。
我的最终目标是使用powershell获取上述屏幕截图中的所有权限。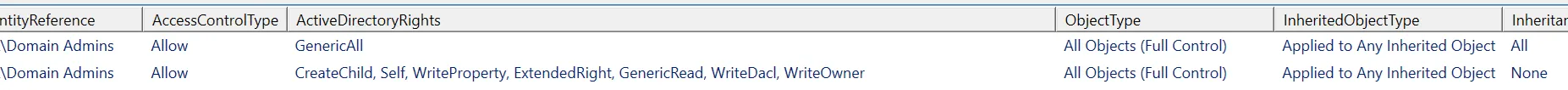
Get-Acl应该给你提供那些信息。使用分组运算符(..)来公开该代码属性。(Get-ACL .\).Access。您可以澄清一下“有效权限”是什么意思吗? - Abraham Zinala