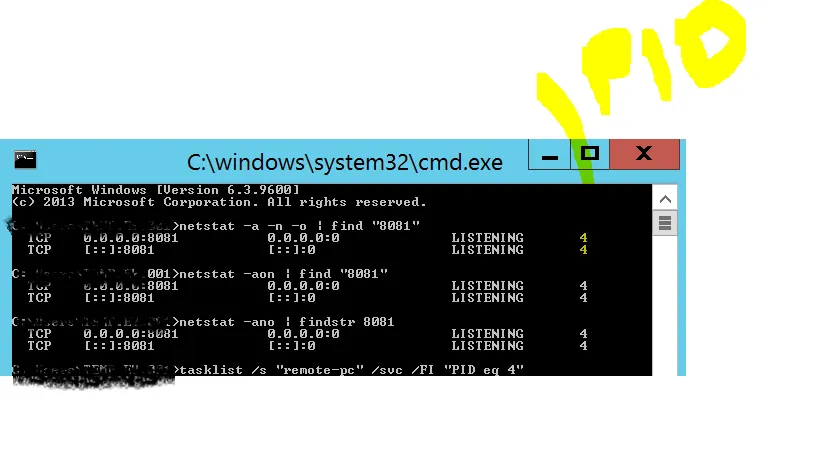
我有一个案例,服务器(dusxxxiweb2)检测到一个漏洞,指出端口8081已打开。我通过netstat -a -n -o | find "8081"命令获取了端口号,发现端口"8081"被PID为4的系统进程使用。
我想知道哪个系统进程使用了这个服务。在此服务器上未安装IIS,但是我可以像下面这样访问一个登录页面(.Net应用程序)。我不知道没有IIS如何实现这一点。
http://dusxxxiweb2:8081/login
我想阻止该端口以解决漏洞问题。在这种情况下我该怎么做?
端口8081被系统(PID 4)占用,如何停止该进程?
4
- vmb
3
如果连IIS都没有安装,那么这个问题就与IIS无关了。HTTP服务(http.sys)是Windows组件,任何应用程序都可以连接它并执行HTTP通信(对于.NET应用程序,自托管就足够了)。调试哪个应用程序是不容易的,但是像保留的URL之类的东西可能会有所帮助 https://docs.jexusmanager.com/tutorials/https-binding.html#reserved-urls 您可以通过在Windows防火墙中添加规则来轻松阻止此类操作。 - Lex Li
@Lex Li..你是说所有的HTTP连接都使用8081端口...我如何将端口更改为HTTP服务的不同端口?这会对任何系统服务造成影响吗? - vmb
显然我没有说你输入的内容。它只是一个连接到该端口并处理HTTP请求的应用程序。除非此应用程序提供更改设置,否则您无法更改端口。它当然会对Windows产生影响(例如CPU使用率,内存使用率),进而影响其他系统服务,但我不确定您要求什么。讨论这样的问题太广泛了,特别是当它与编程无关,更多地涉及网络/配置/安全问题时。您实际的目标(如安全问题)在这里非常重要,因为这决定了您接下来可能要做什么。 - Lex Li
1个回答
12
运行命令:
netsh http show servicestate view=requestq,会给出所有HTTP监听器的快照。找到包含所需端口号的“Registered URL”,控制进程的PID将在其上方数行,就像我的恶意进程一样;Request queue name: Request queue is unnamed.
Version: 2.0
State: Active
Request queue 503 verbosity level: Basic
Max requests: 1000
Number of active processes attached: 1
--> Process IDs:
14035
URL groups:
URL group ID: F80000014000004F
State: Active
Request queue name: Request queue is unnamed.
Properties:
Max bandwidth: inherited
Max connections: inherited
Timeouts:
Timeout values inherited
Number of registered URLs: 1
--> Registered URLs:
HTTP://+:8081/ROGUESERVICE/
Server session ID: F70000011000012D
Version: 2.0
State: Active
Properties:
Max bandwidth: 4294967295
Timeouts:
Entity body timeout (secs): 120
Drain entity body timeout (secs): 120
Request queue timeout (secs): 120
Idle connection timeout (secs): 120
Header wait timeout (secs): 120
Minimum send rate (bytes/sec): 150
- L1ttl3J1m
网页内容由stack overflow 提供, 点击上面的可以查看英文原文,
原文链接
原文链接